Advertising procedure of entrepreneurs should be conservative, powerful and ought to have the option to procure exceptional yields. The World Wide Web offers rewarding showcasing choices to every one of the advertisers and the best one includes making a business website. Entrepreneurs cannot contribute a great deal of time and cash in getting a specially crafted website, however they can utilize a website maker to make proficient websites rapidly and without any problem. A website maker is incredibly simple to utilize and permits building website in a matter of moments. Allow us to take a gander at a portion of the reasons that settle on website makers the ideal decision for entrepreneurs.
- Premade Template Designs
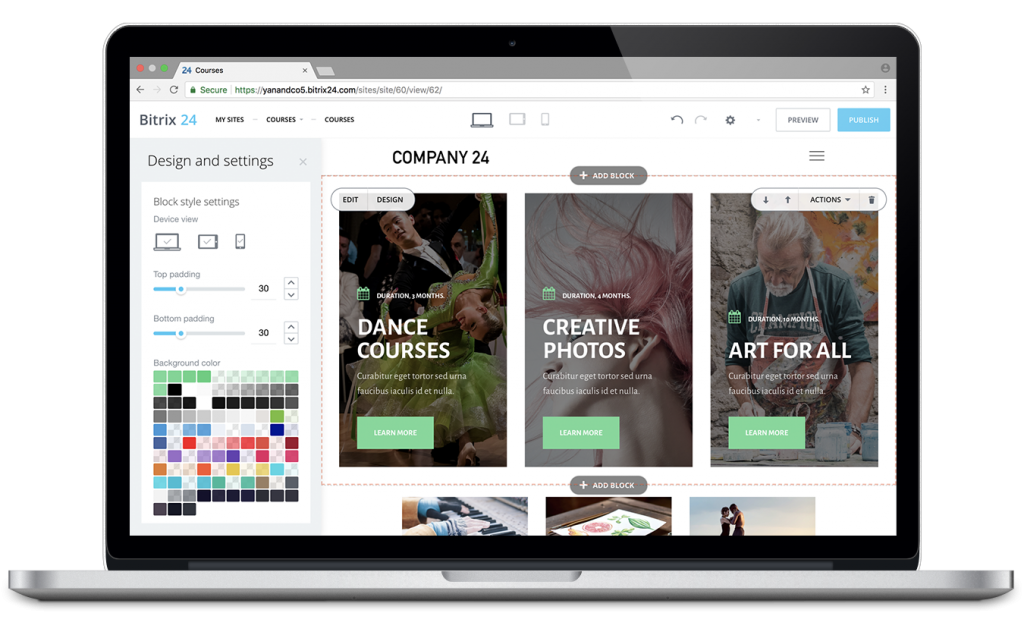
Website makers offer an exhibit of premade business layouts that are explicit to different business verticals. Clients can pick a plan and shading theme that totally coordinates with their business persona and make a website. This load of plans are made by experienced and proficient planners and specialty a shocking and alluring appearance. It saves entrepreneurs both time and cost spent in employing originators and getting a hand craft.
- Simple To-Use
All the website makers give a natural and easy to use content administration framework that can be utilized and overseen easily. It does not need any specialized expertise and permits anyone to assemble a website. You can add fascinating components like Google maps, Google investigation and email records to your website through a bit by bit spread out process without utilizing any kind of HTML coding.
- Modified Content
Content is supposed to be the lord in showcasing language. Content is vital for any website and that is the reason most entrepreneurs employ content scholars or expert essayists to make content for their websites though a premade layout comprises of industry-explicit substance for every vertical. The substance is additionally stacked with well-informed catchphrases to get the website a higher positioning on different web crawlers.
- Site design improvement
When a website gets distributed, get it ordered by significant web crawlers so it is effortlessly found on the web. Website makers embed pertinent meta labels into their web pages with the goal that the website is effortlessly found by the web search tools. These meta labels can likewise be just altered by the clients to make them more fit to their particular business verticals. Consequently, website makers save the expense and time spent on site design improvement by any entrepreneur.
- Stock Images
Websites are deficient without important pictures and photograph exhibitions. Each website maker offers business explicit top notch stock pictures alongside its layouts that are most appropriate for your vertical. These can be supplanted to add more customized pictures, however they do make an expert search for the business websites and save the expense of purchasing stock pictures.
- Free Hosting
For a hand crafted website, proprietors need to discover a web hosting service yet Zyro website builder or Zyro website maker give free hosting service. Other than this load of reasons, least expense and time spent in building a website are likewise the significant purposes for website makers being the ideal decision for entrepreneurs.



